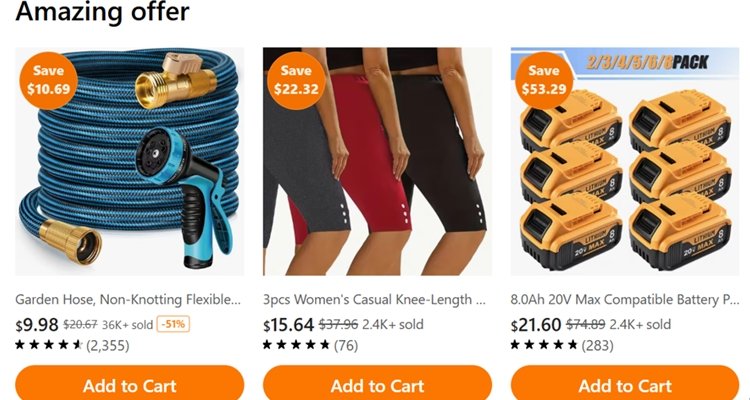
At least in free email accounts, Yahoo!mail often places advertisements above the list of received email. The ad looks like another email header. But if you click on a recent Yahoo!mail ad promoting a Temu Clearance Sale, you are taken not to an email about the sale but directly to the Temu web site, which touts things like garden hoses, women’s wear, and batteries.
Some of the many deals look suspicious, and Temu costumers sometimes complain about cheap prices being matched by cheap quality. But the deals aren’t the problem.
Worse than TikTok
A couple of years ago, The Federalist argued that “Communist China–Connected Temu Is Worse Than TikTok” (July 1, 2024). The author is talking about the app.
“Once downloaded, Temu can access almost anything on your phone—the camera, internet, audio recordings, and more—according to one study.”
I didn’t download any app, only glanced at the Temu website long enough to grab the above screenshot. So I (think I) am safe. But what if I were a regular user of the app, currently available in the Apple and Google Play app stores?
A recent report revealed that top Temu executives—including executives overseeing their public and legal affairs, public relations, and operations—are former high-ranking officials of the CCP. Perhaps this is one of many reasons why they’re targeting America so heavily with this app and not offering the platform in China….
As revealed by one study, once downloaded, Temu can access almost anything on your phone—the camera, internet, audio recordings, etc. That means the CCP could theoretically install applications and spyware files on an individual’s smart device to use for complete surveillance of all user activity on a phone. This would allow China to monitor keystrokes and logs to have direct insight into login credentials for other social media, emails, and bank accounts.
In other words, Temu can just as accurately be called a malware program as an e-commerce platform. No wonder Temu’s CCP-veteran executives are willing to lose $30 an order. Furthermore, Temu’s parent company, PDD, was removed from Google Play on the grounds that the fraudulent app had harmful malware that captured highly sensitive personal information, including biometrics, geolocation, and more. And it is common practice for China to refine its cyberattack tactics once exposed to be not only more virulent but more hidden.
Part of this report looks out of date. Perhaps the Temu app was once booted from the Google Play store. It’s there now. Persons considering whether to download it are advised: “This app may share these data types with third parties: Device or other IDs. This app may collect these data types: Location, Personal info and 5 others.”
Five others? Inquiring minds want to know.
Also see:
Grizzly Research: “…Shopping App TEMU Is Cleverly Hidden Spyware…”
“If all the rest of the objectionable code was removed while this one backdoor went undetected due to its concealment, the app could become just as malignant by changing its behavior, controlled by foreign servers….”












