The Republic of China reported in 2025 that its government departments were coping with something like 2.8 million cyberattacks per day. If we assume that this number of average daily attacks is more or less accurate, can we also reasonably assume that each attack is individually tailored? No. Probably a lot of automation must be involved.
Hackers’ automated attacks are being helped by AI tools good at finding and exploiting weaknesses. Hack Read reports on what SOCRadar, a cybersecurity firm, has learned about a “massive, automated cybercrime setup linked to threat actors based in China” (May 1, 2026).
One element of the setup is OpenClaw, an AI assistant that can perform tasks, not just provide information in response to questions; a sort of macro or script on steroids. If, as an innocent user, you configure OpenClaw imperfectly, it might screw up your stuff. The cyberattackers, being malicious, use it and other tools to screw up your stuff deliberately.
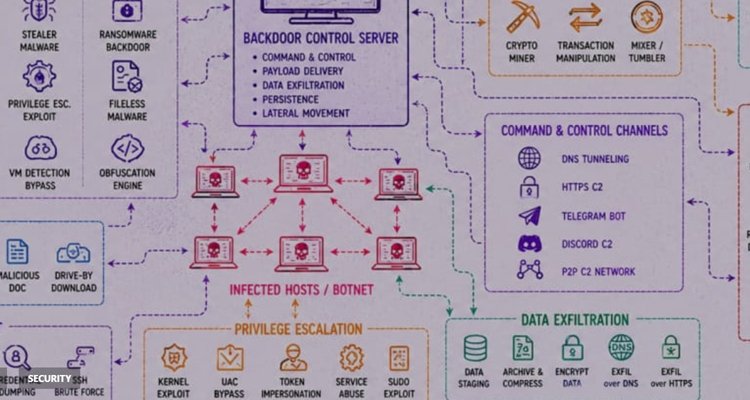
Hackers use internet mapping engines such as FOFA and 360Quake [both developed by firms based in China] to identify the External Attack Surface (internet-facing assets). They particularly target high-value groups like fintech companies, Web3 platforms, and security vendors….
This scanning helps them find systems running software with known security flaws…..
After achieving initial access, the threat actors search for sensitive data…. To maintain persistence, they use several methods to ensure they stay hidden…
The group also uses a fileless execution chain using commands that feed web content directly into Node.js to run malicious code in the system’s memory without saving any files to the disk. This makes malware detection much more difficult….
This is a very large operation. The hackers’ own logs show around 45,000 attack attempts. Their database shows they have placed the d2 backdoor on 3,981 hosts and the pl backdoor on 1,393 hosts. They also managed 900 webshell implants and are tracking nearly 22,000 cryptocurrency addresses.
“The operation is coordinated through a centralised backend,” the report explains, which helps the group manage and enrich stolen data. The hackers use blockchain intelligence APIs such as OKLink and Tatum to monitor nearly 22,000 cryptocurrency addresses. They also use automated scripts to validate stolen Stripe keys by checking for active accounts with available balances. This organised approach allows the threat actors to immediately prioritise the most profitable targets.
Hack Read stops there. SOCRadar adds that it can help if your online operation is one of those being targeted. It provides “Dark and deep web monitoring…attack surface management…supply chain intelligence…threat actor tracking…. If your organization operates in Web3 [related to cryptocurrencies and blockchains], fintech, or cloud-native environments, you are a high-priority target for this class of threat actor.”
The analysts don’t compare the Chinese hackers’ use of agentic AI to detect vulnerabilities for criminal purposes to the potential of Anthropic’s much-publicized Claude Mythos—to be used, Anthropic hopes, only to fix vulnerabilities and prevent crime.












